�������: 16-30 ���鵽��Strategy����ؼ�¼526�� . ��ѯʱ��(0.407 ��)
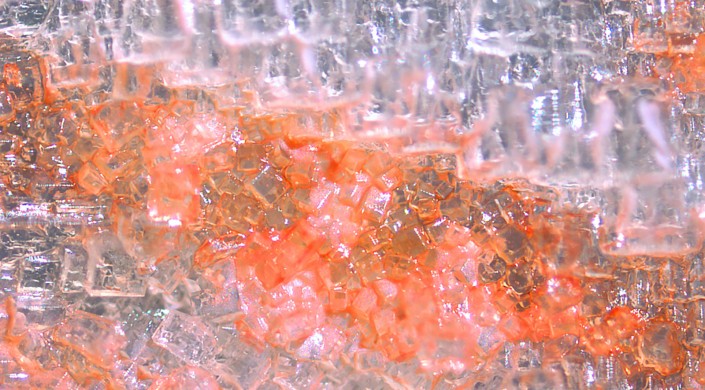
Emergent Protective Organogenesis in Date Palms: A Morpho-devo-dynamic Adaptive Strategy During Early Development
Phoenix dactylifera L. emergent protective desert plants early organogenesis organ-specific cell
2024/3/4
Desert plants have developed mechanisms for adapting to hostile desert conditions, yet these mechanisms remain poorly understood. Here, we describe two unique modes used by desert date palms (Phoenix ...
Serendipity and strategy:the growth of Linguistics at Victoria
anniversary sociolinguistics
2019/10/10
I was born a Lancashire lass and spent my first eighteen years living in a small village,Formby, located between Liverpool, the big smoke for us, and Southport, a rather genteel holiday resort where t...
Practical Strategy-Resistant Privacy-Preserving Elections
cryptographic protocols Privacy voting
2018/11/19
Recent advances in cryptography promise to let us run complex algorithms in the encrypted domain. However, these results are still mostly theoretical since the running times are still much larger than...
With an historian��s keen eye for detail and nuance, John Lewis Gaddis surveys a variety of case studies from the Peloponnesian War to World War II in his new book On Grand Strategy, identifying in the...
Economic and Financial Sanctions in U.S. National Security Strategy
U.S. National Security Strategy Economic Financial Sanctions
2019/10/11
Coercive U.S. strategies often feature the use of economic and financial sanctions to address national security threats. According to the most recent U.S. National Security Strategy, sanctions and oth...
A GUIDED REGISTRATION STRATEGY EMPLOYING VIRTUAL PLANES TO OVERCOME NON-STANDARD GEOMETRIES �C USING THE EXAMPLE OF MOBILE MAPPING AND AERIAL OBLIQUE IMAGERY
Mobile Mapping Feature Matching Image Orientation Oblique Imagery
2018/6/4
Mobile mapping (MM) is an intriguing as well as emerging platform and technology for geo-data acquisition. In typical areas of interest for MM campaigns, such as urban areas, unwanted GNSS multipath, ...
Analysis on exploitation status, potential and strategy of groundwater resources in the five countries of Central Asia
The five countries of Central Asia Groundwater Sustainable development
2018/3/23
As an important part of water resources of the five countries of Central Asia, groundwater resources give critical supports to the regional economic development. Accompanied by rapid economic developm...
����������ѧ��ҵս�Թ���Ӣ�Ŀμ�Chapter 8
Strategy Implementation and Control
����������ѧ ��ҵս�Թ��� Ӣ�Ŀμ� Chapter 8
Strategy Implementation and Control
2018/3/14
����������ѧ��ҵս�Թ���Ӣ�Ŀμ�Chapter 8
Strategy Implementation and Control��
����������ѧ��ҵս�Թ���Ӣ�Ŀμ�Chapter 6 International Strategy
����������ѧ ��ҵս�Թ��� Ӣ�Ŀμ� Chapter 6 International Strategy
2018/3/14
����������ѧ��ҵս�Թ���Ӣ�Ŀμ�Chapter 6 International Strategy��
����������ѧ��ҵս�Թ���Ӣ�Ŀμ�Chapter 6 Corporate-level Strategy :
Diversification
����������ѧ ��ҵս�Թ��� Ӣ�Ŀμ� Chapter 6 Corporate-level Strategy :
Diversification
2018/3/14
����������ѧ��ҵս�Թ���Ӣ�Ŀμ�Chapter 6 Corporate-level Strategy :
Diversification��
����������ѧ��ҵս�Թ���Ӣ�Ŀμ� Dynamic Competitive Strategy
����������ѧ ��ҵս�Թ��� Ӣ�Ŀμ� Dynamic Competitive Strategy
2018/3/14
����������ѧ��ҵս�Թ���Ӣ�Ŀμ� Dynamic Competitive Strategy��
����������ѧ��ҵս�Թ���Ӣ�Ŀμ�Chapter 4 Business-Level Strategy
����������ѧ ��ҵս�Թ��� Ӣ�Ŀμ� Chapter 4 Business-Level Strategy
2018/3/14
����������ѧ��ҵս�Թ���Ӣ�Ŀμ�Chapter 4 Business-Level Strategy��
����������ѧ��ҵս�Թ���Ӣ�Ŀμ�Chapter 1 Introduction: Corporate strategy and strategic management
����������ѧ ��ҵս�Թ��� Ӣ�� �μ� Chapter 1 Introduction: Corporate strategy strategic management
2018/3/14
����������ѧ��ҵս�Թ���Ӣ�Ŀμ�Chapter 1 Introduction: Corporate strategy and strategic management��
Cellular Division Strategy Shared Across All Domains Of Life��ͼ��
Cellular Division Strategy Shared All Domains Of Life
2018/1/10
The three domains of life �� archaea, bacteria, and eukarya �� may have more in common than previously thought.Over the past several years, Ariel Amir, Assistant Professor in Applied Mathematics at the ...
On the Strategy and Behavior of Bitcoin Mining with N-attackers
Bitcoin Mining Selfish mining
2018/1/2
Selfish mining is a well-known mining attack strategy discovered by Eyal and Sirer in 2014. After that, the attackers' strategy space has been extended by many works. These works only analyze the stra...
�й��о����������а�-��
- ���ڼ���...
�й�ѧ���ڿ����а�-��
- ���ڼ���...
�����ѧ���л������а�-��
- ���ڼ���...
�й���ѧ���а�-��
- ���ڼ���...
�ˡ���-ƪ
- ���ڼ���...
�Ρ���-ƪ
- ���ڼ���...
��������-ƪ
- ���ڼ���...
�������� -ƪ
- ���ڼ���...
֪ʶҪ��-ƪ
- ���ڼ���...
���ʶ�̬-ƪ
- ���ڼ���...
��������-ƪ
- ���ڼ���...
ѧ��ָ��-ƪ
- ���ڼ���...
ѧ��վ��-ƪ
- ���ڼ���...

