搜索结果: 1-15 共查到“weaknesses”相关记录37条 . 查询时间(0.062 秒)
3D MODELS FOR ALL: LOW-COST ACQUISITION THROUGH MOBILE DEVICES IN COMPARISON WITH IMAGE BASED TECHNIQUES. POTENTIALITIES AND WEAKNESSES IN CULTURAL HERITAGE DOMAIN
Structure from Motion Image Based Modelling Mobile devices 3D Imaging Representation Techniques
2018/3/6
Nowadays, 3D digital imaging proposes effective solutions for preserving the expression of human creativity across the centuries, as well as is a great tool to guarantee global dissemination of knowle...
Password-based key derivation functions are of particular interest in cryptography because they (a) input a password/passphrase (which usually is short and lacks enough entropy) and derive a cryptogra...
Weaknesses in Hadamard Based Symmetric Key Encryption Schemes
secret-key cryptography Symmetric Key Encryption Schemes
2016/2/24
In this paper security aspects of the existing symmetric key encryption schemes based
on Hadamard matrices are examined. Hadamard matrices itself have symmetries like one
circulant core or two circu...
Logical Reasoning to Detect Weaknesses About SHA-1 and MD4/5
Logical cryptanalysis MD5 SHA-1 Satisfiability
2016/1/23
In recent years, studies about the SATisfiability Problem (short for SAT) were more and more numerous because of its conceptual simplicity and ability to express a large set of various problems. Wit...
Weaknesses of Password Authentication Scheme Based on Geometric Hashing
cryptographic protocols authentication schemes
2016/1/23
We show that a recently proposed password authentication scheme based on geometric hashing has several security weaknesses, and that the use of this scheme should be avoided in practice.
Statistical weaknesses in 20 RC4-like algorithms and (probably) the simplest algorithm free from these weaknesses - VMPC-R
PRNG CSPRNG RC4
2016/1/23
We find statistical weaknesses in 20 RC4-like algorithms including the original RC4, RC4A, PC-RC4 and others. This is achieved using a simple statistical test. We found only one algorithm which was ...
The BRUTUS automatic cryptanalytic framework: Testing CAESAR authenticated encryption candidates for weaknesses
Authenticated Encryption CAESAR BRUTUS
2016/1/6
This report summarizes our results from security analysis covering all 57 competitions for authenticated encryption: security, applicability, and robustness (CAESAR) first-round candidates and over 21...
Key recovery attacks on Grain family using BSW sampling and certain weaknesses of the filtering function
Stream cipher Grain cipher State recovery attack
2016/1/5
A novel internal state recovery attack on the whole Grain family of ciphers is
proposed in this work. It basically uses the ideas of BSW sampling along with employing
a weak placement of the tap pos...
Security Weaknesses of an "Anonymous Attribute Based Encryption" appeared in ASIACCS'13
Attribute Based Encryption Anonymity Anonymous Encryption
2016/1/5
Attribute-based Encryption (ABE) has found enormous application in
fine-grained access control of shared data, particularly in public cloud. In 2013, Zhang et al proposed a scheme called match-then-d...
Structural Weaknesses in the Open Smart Grid Protocol
protocol analysis authentication protocol OSGP
2016/1/4
The Open Smart Grid Protocol (OSGP) is currently deployed in various countries in
large-scale Smart Metering projects. The protocol was developed by the OSGP Alliance
and published as a standard by ...
The Bookmark Procedure for Setting Cut-Scores and Finalizing Performance Standards:Strengths and Weaknesses
Setting Cut-Scores Finalizing Performance Standards Strengths and Weaknesses
2015/9/15
The Bookmark standard-setting procedure was developed to address the perceived problems with the most popular method for setting cut-scores: the Angoff procedure (Angoff, 1971). The purposes of this a...
OBJECT-BASED IMAGE ANALYSIS:STRENGTHS,WEAKNESSES,OPPORTUNITIES AND THREATS (SWOT)
object-based image analysis (OBIA) Strengths Weakness Opportunities and Threats (SWOT)
2015/8/19
As an emerging discipline, we propose a formal definition of OBIA, describe how OBIA came into existence, and as a road map to future research propose a fundamental objective. In order to provide pote...
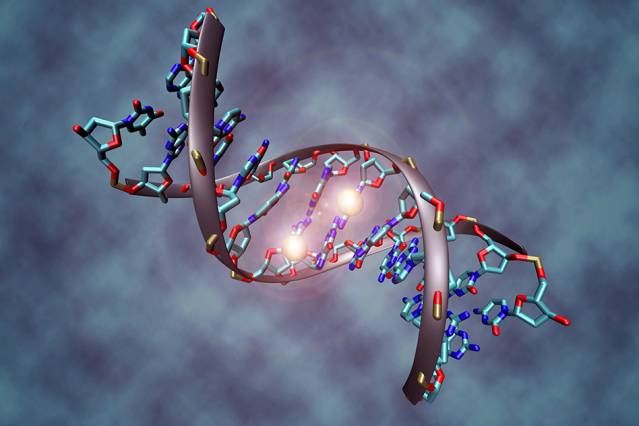
Scientists have known for decades that cancer can be caused by genetic mutations, but more recently they have discovered that chemical modifications of a gene can also contribute to cancer. These alte...
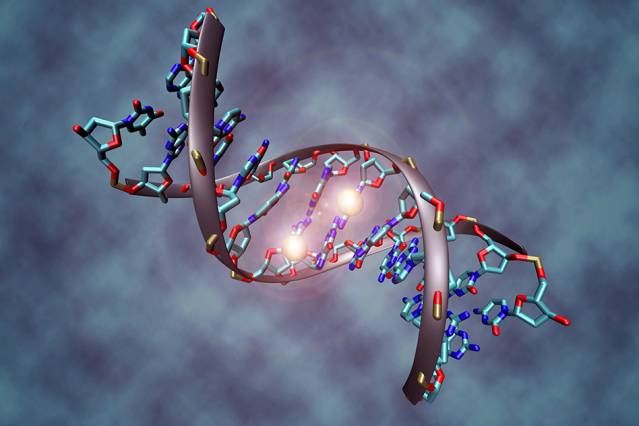
Scientists have known for decades that cancer can be caused by genetic mutations, but more recently they have discovered that chemical modifications of a gene can also contribute to cancer. These alte...
Weaknesses in a Recently Proposed RFID Authentication Protocol
RFID Authentication Security, Privacy
2014/3/5
Many RFID authentication protocols have been proposed to provide desired security and privacy level for RFID systems. Almost all of these protocols are based symmetric cryptography because of the limi...

