搜索结果: 1-15 共查到“TAG”相关记录49条 . 查询时间(0.062 秒)
中科院上海硅酸盐所在铽铝石榴石(TAG)基磁光陶瓷方向取得系列研究进展(图)
陶瓷 核聚变 激光医疗
2024/10/11
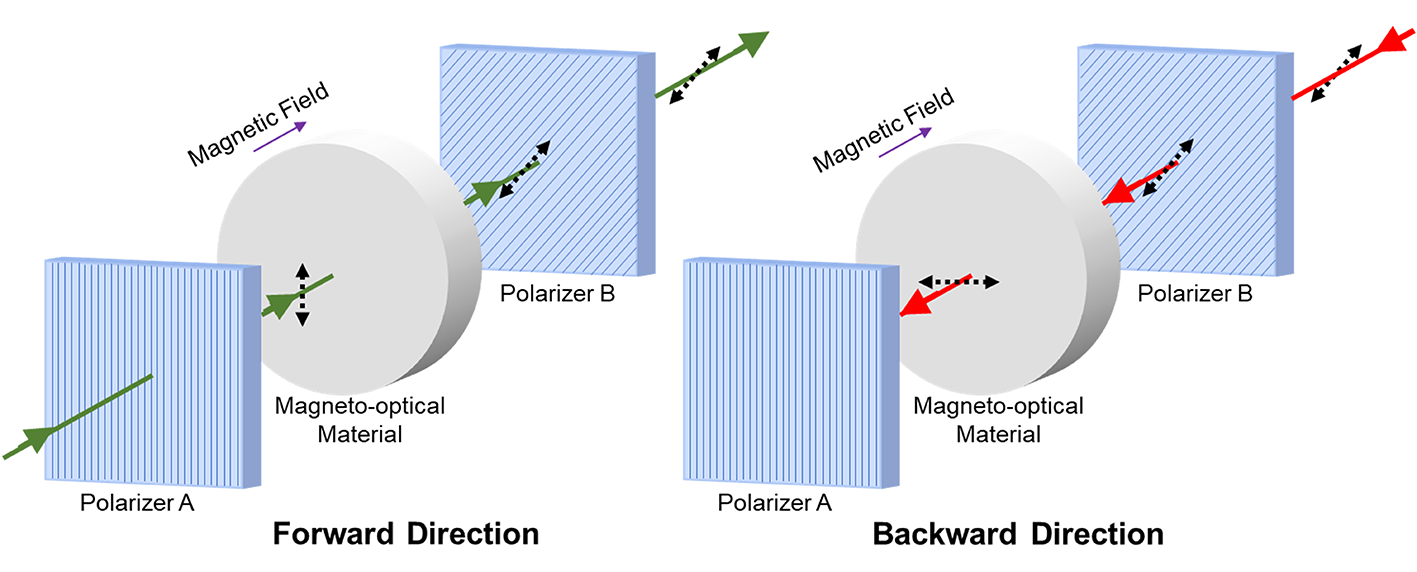
随着激光技术和激光系统的快速发展,激光器已在激光加工、引力波探测、惯性约束核聚变、激光医疗、科学研究等领域发挥了重要作用,如今人们进一步对激光器的性能提出了更高要求。通常,出射激光被物体反射后,会对前端系统造成干扰甚至损伤,影响激光器的稳定工作,而采用磁光隔离器可以有效地解决这一问题。磁光材料是光隔离器的核心部件,其利用法拉第效应,在磁场作用下使入射光的偏振面发生偏转,实现激光的正向通过与反向隔离...

近日,第二医院血管外科率先完成全国首例运用GORE TAG可主动调控胸主动脉覆膜支架系统CTAG with Active control Deployment System(CADS)弓部原位开窗治疗A型主动脉夹层手术。此病例以脑供血保护为关键,以双功管连接颈动脉-股动脉,保证颅内供血;运用一步法肝穿针进行原位开窗,预扩充分后用VBX球扩支架重建弓上二分支;运用GORE TAG可主动调控胸主动脉覆...
华中农业大学李兴旺教授课题组首次建立植物单细胞核CUT&Tag方法(图)
华中农业大学 李兴旺 植物单细胞核
2021/12/31
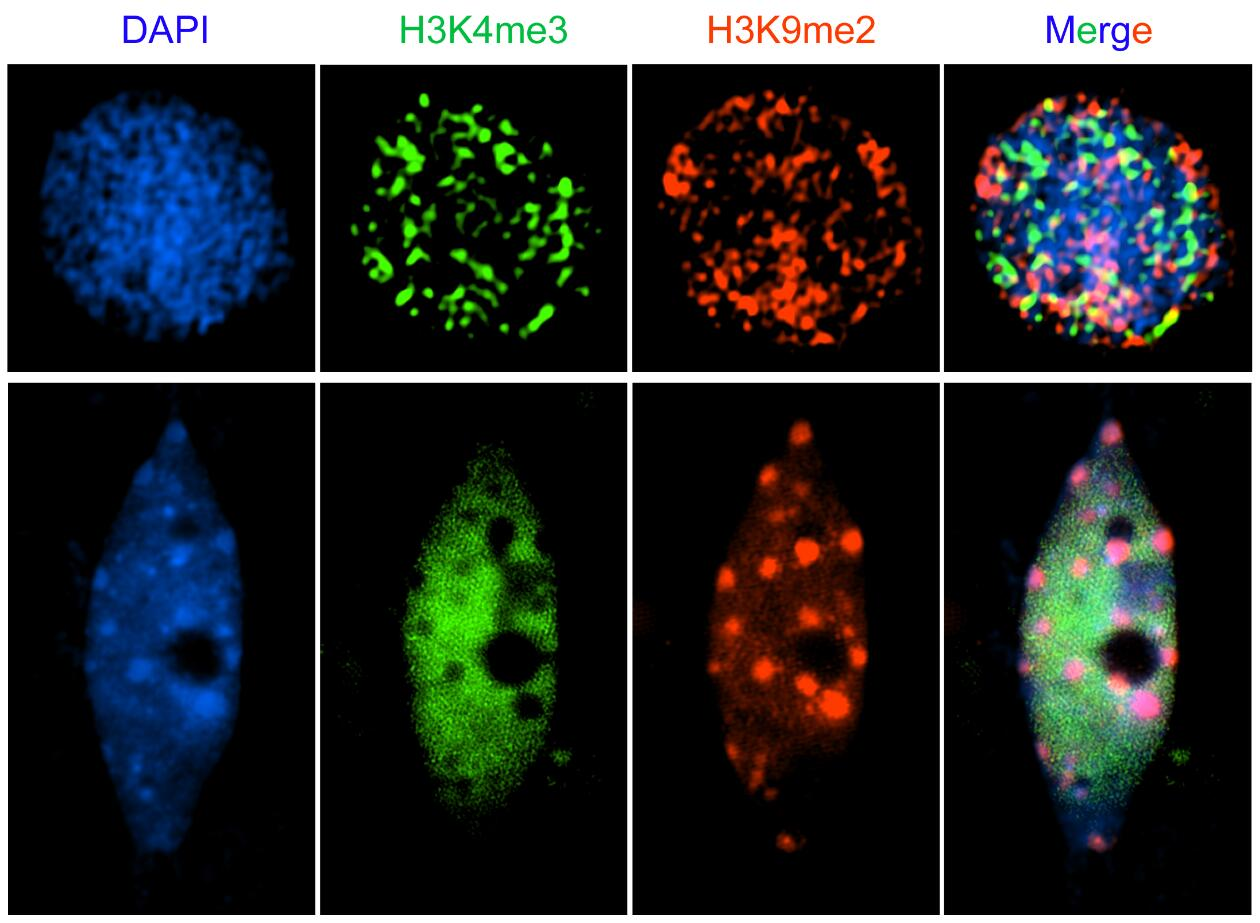
近日,华中农业大学作物遗传改良国家重点实验室李兴旺课题组研究成果以“Profiling Plant Histone Modification at Single-cell Resolution Using snCUT&Tag”为题在Plant Biotechnology Journal。研究首次报道了在植物中建立了单细胞核CUT&Tag (snCUT&Tag)方法,可以高通量分析单个细胞核的组蛋白...
Privacy of Stateful RFID Systems with Constant Tag Identifiers
RFID scheme security privacy
2019/7/18
There is a major interest in designing RFID schemes based on symmetric-key cryptography and ensuring efficient tag identification. These requirements taken together often lead to a decrease in the deg...
Reconsidering Generic Composition: the Tag-then-Encrypt case
Authenticated Encryption generic composition tag-then-encrypt
2018/11/5
Authenticated Encryption (AEAE) achieves confidentiality and authenticity, the two most fundamental goals of cryptography, in a single scheme. A common strategy to obtain AEAE is to combine a Message ...
ABE with Tag Made Easy: Concise Framework and New Instantiations in Prime-order Groups
Attribute-based encryption Predicate encoding Prime-order bilinear group
2017/9/13
Among all existing identity-based encryption (IBE) schemes in the bilinear group, Wat-IBE proposed by Waters [CRYPTO, 2009] and JR-IBE proposed by Jutla and Roy [AsiaCrypt, 2013] are quite special. A ...
Super-Strong RKA Secure MAC, PKE and SE from Tag-based Hash Proof System
related-key attack hash proof system message authentication code
2016/12/7
In this paper, we define new RKA security notions for several cryptographic primitives including message authentication code (MAC), public-key encryption (PKE) and symmetric encryption (SE). This new ...
A Tag Based Encoding: An Efficient Encoding for Predicate Encoding in Prime Order Groups
encodings prime order groups inner product encryption
2016/6/29
We introduce a tag based encoding, a new generic framework for
modular design of Predicate Encryption (PE) schemes in prime order groups. Our
framework is equipped with a compiler which is adaptivel...
Rapid Isolation of Bacterial Photosynthetic Reaction Centers with an Engineered Poly-Histidine Tag
photosynthetic reaction center poly-histidine tag isolation method (bacterium)
2016/5/23
A very rapid method for isolating bacterial photosynthetic reaction centers (RCs) of high purity and yield is described. A poly-histidine tag is engineered at the C-terminus of the RC M-subunit, allow...
On the Security of the Algebraic Eraser Tag Authentication Protocol
Algebraic Eraser cryptanalysis tag authentication
2016/2/23
The Algebraic Eraser has been gaining prominence as SecureRF,
the company commercializing the algorithm, increases its marketing
reach. The scheme is claimed to be well-suited to IoT applications bu...
Efficient Distributed Tag-Based Encryption and its Application to Group Signatures with Efficient Distributed Traceability
Group signatures distributed traceability distributed public-key encryption
2016/1/6
In this work, we first formalize the notion of dynamic group signatures with distributed traceability,
where the capability to trace signatures is distributed among n managers without requiring any i...
Attacks on Secure Ownership Transfer for Multi-Tag Multi-Owner Passive RFID Environments
cryptanalysis anonymity RFID
2016/1/5
Sundaresan et al proposed recently a novel ownership transfer protocol for multi-tag multi-owner RFID environments that complies with the EPC Class1 Generation2 standard. The authors claim that this p...
Tagged One-Time Signatures: Tight Security and Optimal Tag Size
Tagged One-Time Signatures Structure-Preserving Signatures Tight Security Reduction
2015/12/31
We present an efficient structure-preserving tagged one-time signature scheme
with tight security reductions to the decision-linear assumption. Our scheme features
short tags consisting of a single ...
Authenticated Encryption without Tag Expansion (or, How to Accelerate AERO)
Authenticated Encryption Stateful Decryption Provable Security
2015/12/24
Standard form of authenticated encryption (AE) requires the ciphertext to be expanded
by the nonce and the authentication tag. These expansions can be problematic when messages are
relatively short ...
Availability of Real Time GIS and IC Tag for Realization of Universal Map
REAL TIME GIS Universal Map D-GPS VRS-GPS Spatial Information Society IC Tag
2015/12/17
Government and local government have to hurry up to build accessible facilities for elderly people and people with disabilities.Because our country is experiencing an aging society, for example, pedes...

